Carbon Black Workload - Technical Overview
What is VMware Carbon Black Cloud Workload Protection?
VMware Carbon Black Cloud Workload™ delivers advanced protection purpose-built for securing modern workloads to reduce the attack surface and strengthen security posture. This innovative solution combines prioritized vulnerability reporting and foundational workload hardening with industry-leading prevention, detection, and response capabilities to protect workloads running in virtualized, private, and hybrid cloud environments.
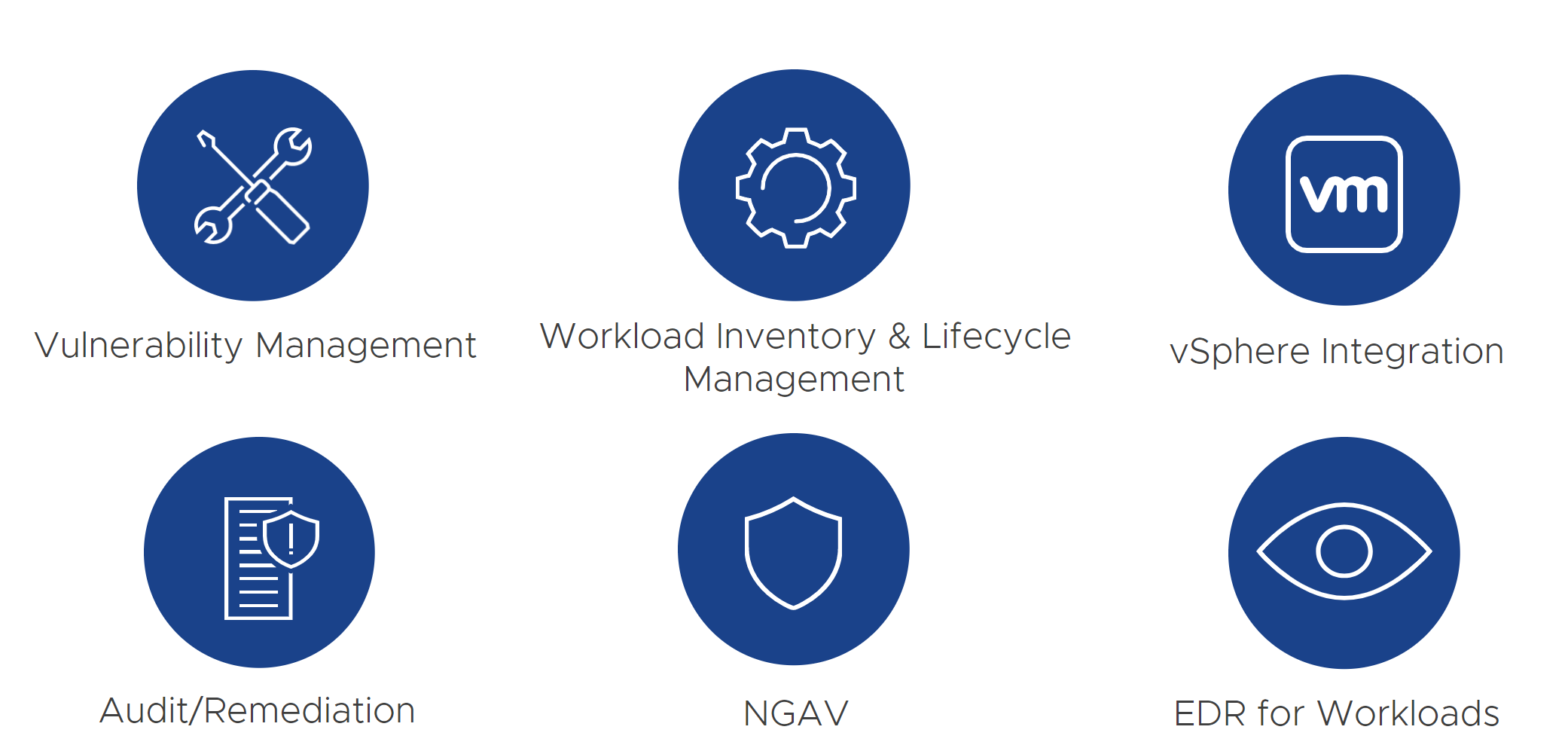
Tightly integrated with vSphere, VMware Carbon Black Cloud Workload provides lightweight sensor-based security that alleviates installation and management overhead and consolidates the collection of telemetry for multiple workload security use cases. This unified solution enables Security and Infrastructure teams to automatically secure new and existing workloads at every point in the security lifecycle while simplifying operations and consolidating the IT and Security stack.
Identify Risk
Initial state integrity check
VMware Carbon Black Cloud conducts an initial state integrity check to validate the system you’re installing the workload on is clean, compliant and appropriate for the type of workload. It will also collect and analyze OS patch levels, assess vulnerabilities and misconfigurations, and determine if additional hardening is required.
Ongoing visibility into system state
VMware Carbon Black Cloud identifies configuration drift, the presence of unknown or unauthorized applications, vulnerabilities, and other dynamic activity that increases the environment’s attack surface.
For example, it will: – Monitor for any changes that indicate nefarious activity (e.g., zeroing out passwords, changes in BitLocker configuration) – Audit and remediate to query 1,500 artifacts for each workload and endpoint across private and public clouds – Empower admins to run custom SQL queries to look out for specific malicious behavior or activity
Ongoing visibility into vulnerabilities and network activity
VMware Carbon Black Cloud enables vSphere admins to view risk-prioritized workload vulnerabilities in VMware vCenter® and regularly run scan-free vulnerability assessments across workloads. NSX delivers a built-in distributed firewall, so IT Ops teams can monitor communication of workloads across private and public clouds, determine which workloads are part of an app, and determine how to segment unrelated workloads.
Prevent risks from escalating
Prevent exploits on the workload
VMware Carbon Black Cloud delivers next-generation antivirus (NGAV) for protection that transcends point-in-time indicators for malware, ransomware, zero-day, rapid variants, suspicious files, and potentially unwanted processes (PUPs) specific to workloads across private and public clouds. The VMware platform combines ransomware decoys, dynamic analysis, and machine learning to provide ongoing analysis that prevents suspicious files from executing.
Prevent non-malware attacks
In addition to blocking malware attacks, VMware Carbon Black Cloud protects against the latest persistent attacks using fileless malware, memory-based, and living-off-the-land (LotL) tactics. These pernicious attacks use existing software and allowlisted apps (e.g., PowerShell), and authorized protocols to carry out malicious activities. Unlike legacy approaches that rely on known threats, the VMware platform can identify new variants and zero-day exploits by piecing together connected behaviors.
Customize prevention
Every environment has different and often competing operational constraints. VMware offers our customers the ability to balance security and operational risks with precise granularity. With the Carbon Black Cloud policy engine, you can choose how to mitigate threats based on the specific type of workload, its function, criticality, and adjacency to other critical workloads.
For example, to isolate a mission-critical workload, a sysadmin can prevent PowerShell from scraping the memory of another process or invoking an untrusted application.
Detect and respond to ongoing risks
Know when and where to start an investigation (zoom in)
Use VMware out-of-the-box automated threat detection via updated threat intelligence from the VMware Threat Analysis Unit™ to pinpoint affected systems and isolate them for remediation. VMware APIs allow you to integrate your own third-party feeds and watchlists, and round out collaborative threat sharing information from VMware’s robust user exchange.
See the full scope and time frame of the attack (zoom out)
The VMware platform allows investigators to rewind the tape to understand how an attack unfolded, which systems were affected, and how the attack progressed over time. Because VMware captures all the data (e.g., detailed process activity, process-to-process interaction, parent-child process relationships, etc.), building a detailed timeline without blind spots—well after the fact—empowers incident response and forensic teams to get to the truth.
Rapid detect-to-prevent workflow
In three easy steps, VMware Carbon Black Cloud enables you to translate threat detection into standardized prevention policy across your workloads.
- Apply automated policies based on previous detections customized for your workloads.
- Preview the downstream effects of the prevention policy before it’s implemented.
- Roll out the updated policy across workloads on any environment.
What are the Key Benefits of Workload Protection?

Benefits for Infrastructure Teams
- Assess vulnerabilities in real time from the vSphere Client
- Increase patching efficiency with best-inclass prioritization
- Leverage security that’s built into your existing infrastructure
- Establish proactive IT hygiene to prevent breaches
- Reduced overhead; no additional infrastructure or heavy scans required
- Replace legacy antivirus on servers to regain compute cycles
Benefits for Security Teams
- Protect workloads from known and unknown attacks
- Reduce complexity by consolidating security tools
- Easily investigate security incidents
- Visualize attack chains in real time
- Faster mean time to resolution (MTTR)
- Remove barriers between security analysis and IT operations
- Engage with an active user community of internal security experts and peers
Top 5 things you should know about Workload Protection
This section helps you understand how Workload Protection will work for you.
- Carbon Black Cloud Workload Appliance
-
The appliance is a package of software that lives on the vSphere side. It is a virtual machine that uses Photon OS and an application to route data from vSphere to the Carbon Black Cloud. The Carbon Black Cloud Workload appliance and plug-in is all bundled in a single Open Virtualization Appliance (OVA) that is used for the complete installation.
You must download the Carbon Black Cloud Workload appliance OVA for installation available from the VMware Downloads page.
- Enabling Carbon Black in Your vSphere Environment
-
Carbon Black Cloud Workload appliance is deployed as a virtual appliance (packaged as an OVA file) on any ESXi host in your vCenter Server environment.
After the appliance is deployed, you must register the appliance with the vCenter Server.
You must then configure the appliance to establish a connection between the Carbon Black Cloud console and the on-premises appliance deployed in the vCenter Server.
After the connection is established, the appliance imports the vCenter inventory.
You can then enable Carbon Black on your workloads either through vSphere or Carbon Black Cloud.
- Minimum Hardware and Software Requirements
-
Before you install or upgrade Carbon Black Cloud Workload, your system hardware must meet the following requirements. You must install one Carbon Black Cloud Workload appliance per vCenter Server.
For more information, see Hardware Requirements.
- Scanless Vulnerability Assessment
-
When a vulnerability is announced, traditional scanning tools often require an engineer to create a signature. Once that signature is created they need to push that signature to their customers. Then the customer needs to schedule a scan (hopefully everyone is online/accessible) to identify where this vulnerability exists.
With VMware Carbon Black Cloud we create a virtualized database of your operating system, so that once a vulnerability is announced we are able to instantly correlate across operating systems and applications to identify where you are at risk.. without the added lead time.
-
Risk-Prioritized Vulnerability Assessment
-
Carbon Black Cloud Workload protection helps to identify a high severity exploitable vulnerability that will be categorized by Risk Score. This score is a metric that accurately represents the risk of a given vulnerability in your data center (the actual exploitability of the CVE). It does so by combining CVSS information with proprietary threat data and advanced modeling from Kenna Security.
VMware Carbon Black has integrated Kenna Security’s vulnerability risk scores directly into VMware Carbon Black Cloud Workload. Every vulnerability within VMware Carbon Black Cloud Workload is assigned a risk score of between 0.0 (no risk) and 10.0 (maximum risk). Risk scores are determined by exploitability, impact and level of effort required to exploit.
With Vulnerability Assessment functionality now available directly in the vSphere Client, you can see and instantly prioritize vulnerabilities, allowing you to effectively reduce risk, speed up workflows, and cut down the cost of administration.
Summary and Additional Resources
Conclusion
This document provides you with a good understanding and overview of Carbon Black Cloud Workload Protection and its capabilities. To learn more about the product explore our hands-on lab and TestDrive experience.
Additional Resources
For more information about Workload Protection, explore the Mastering Workload Protection Path. The activity path provides step-by-step guidance to help you increase your understanding of Carbon Workload Protection, including articles, videos, and labs.
Change Log
The following updates were made to this guide:
|
Date |
Description of Changes |
|
2021/09/15 |
|
| 2023/10/17 |
|
Authors and Contributors
With significant contributions from:
- Dale McKay, Manager, Senior Technical Marketing Architect, Carbon Black
- Juliane Neumann, Senior Technical Marketing Manager
